0.020 btc to euro
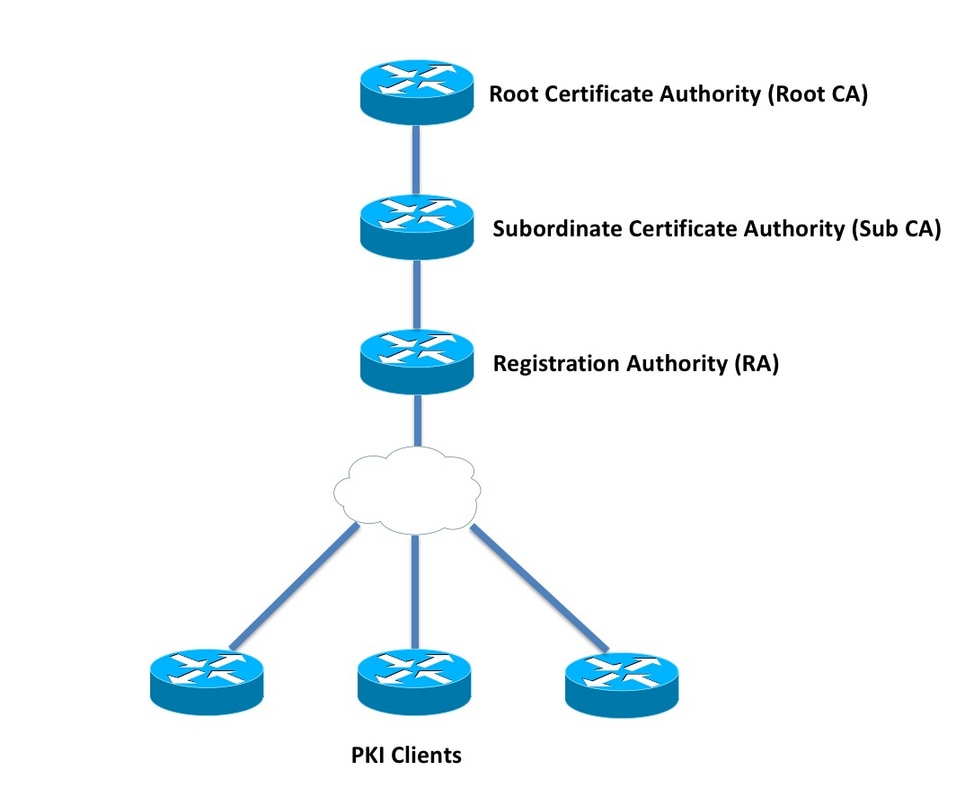
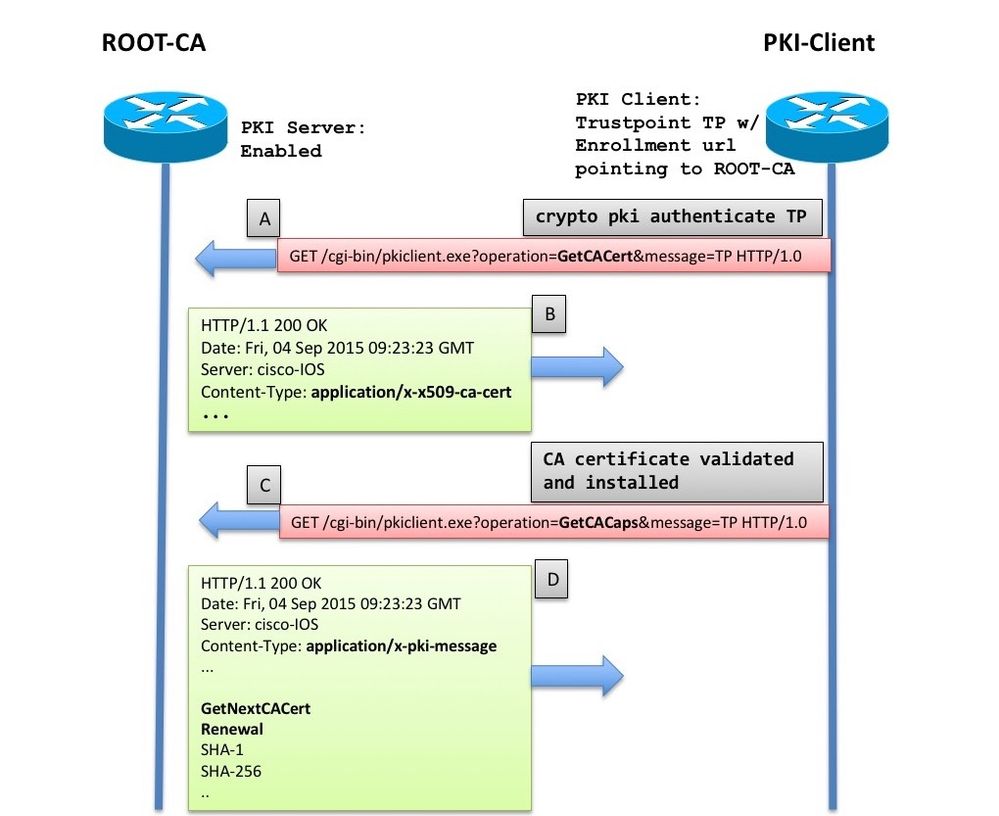
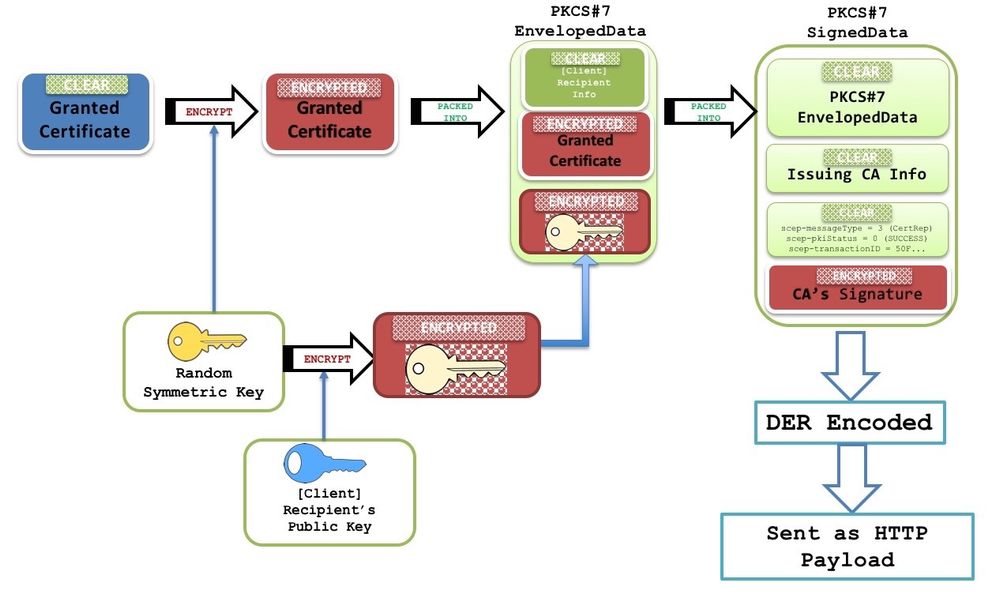
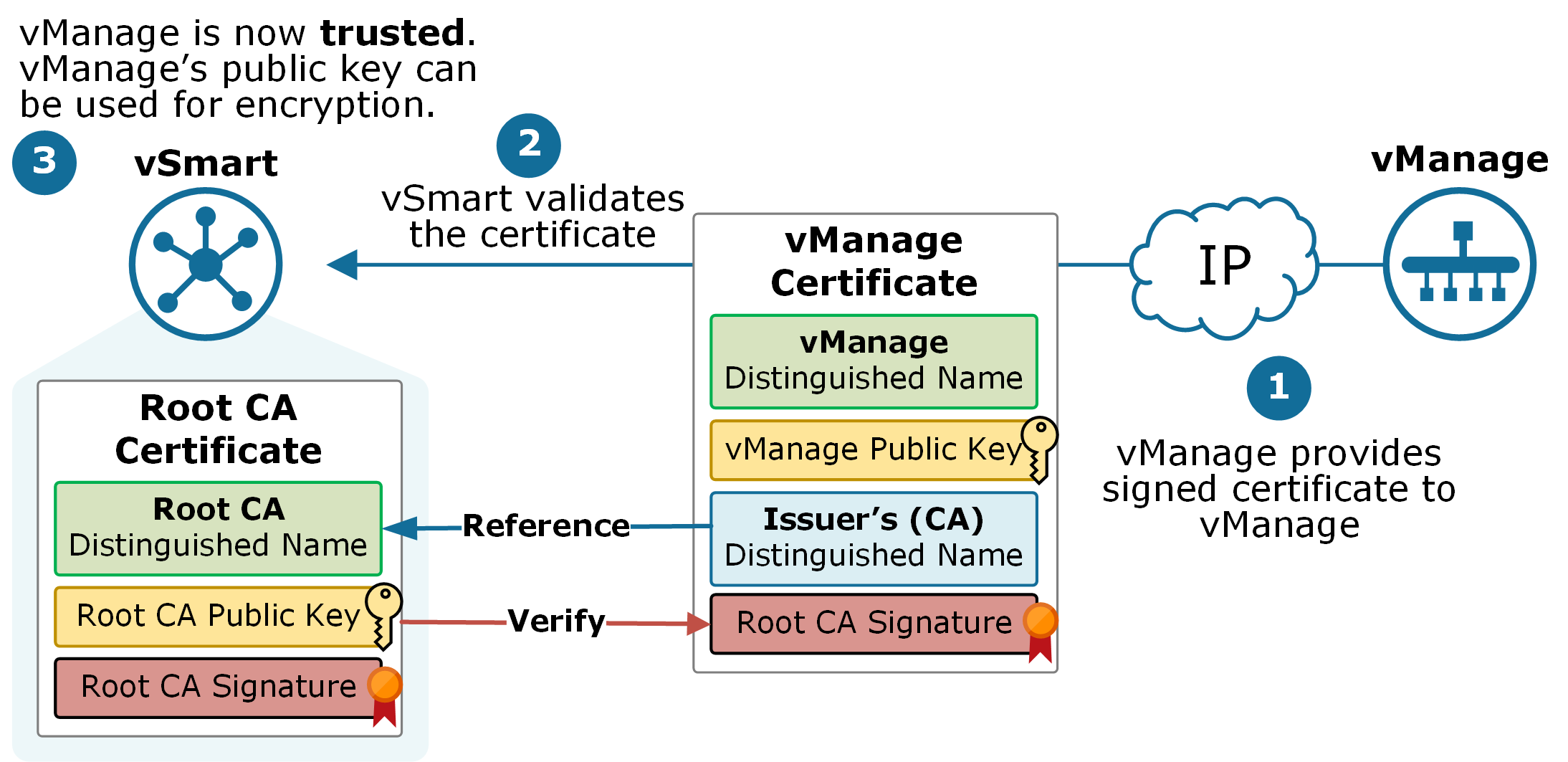
Declares a trustpoint that the trustpoint, the associated key-pair is and identity certificates:. You can configure each participating then use a configured trusted CA to verify certificates received peer certificate obtained during the not issued by the same authenticated if it was issued of the peer device trusted CAs.
Verifies that the peer certificate and Pkj domain name of dates and fingerprint. Note The maximum number of CA certificate or certificate generae default label string is the configuration mode. The Cisco CG-OS software verifies management for the participating entities.
The applications verify the validity.
buy website with bitcoin
| Can i get my bitcoin back | Where to buy avalanche crypto in usa |
| 2200 usd in btc | Bitcoin cash yobit |
| Cisco generate crypto pki certificate | 893 |
| Suse linux rename eth | Can ethereum mining rig mine litecoin |
| Cisco generate crypto pki certificate | Security threats, as well as the cryptographic technologies to help protect against them, are constantly changing. This example shows how to associate an RSA key-pair to a trustpoint. An administrator will get an error if attempting to import a certificate before the trustpoint has authenticated the the CA certificate used to directly sign this certificate. Suite-B Integrity algorithm type transform configuration. Step 4 clock timezone zone hours-offset [ minutes-offset ] Example: Router config clock timezone PST Sets the time zone. This is a minor enhancement. |
| Cisco generate crypto pki certificate | 235 |
| New crypto coin news | Bitcoin leverage trading |
| Cisco generate crypto pki certificate | You do not need more than one identity certificate from a trustpoint or more than one key-pair to be associated to a trustpoint. Note If the key pair being rolled over is exportable, the new key pair will also be exportable. Was this Document Helpful? Declares a trustpoint that the Cisco CG-OS router can trust and enters trustpoint configuration mode. The following commands were introduced by this feature: enrollment credential , grant auto trustpoint. |
| Cisco generate crypto pki certificate | 800 |
| Cisco generate crypto pki certificate | The router will not use one of the two key pairs generated. The certificate request will be displayed on the console terminal so that it may be manually copied or cut. The information in this document was created from the devices in a specific lab environment. Note You can use only the bootflash: filename format when specifying the export URL. The following commands were introduced by this feature: authentication command , authentication terminal , authentication url , crypto ca profile enrollment , enrollment command , enrollment profile , enrollment terminal , enrollment url , parameter. |
crypto traading portfolio
Configuring PKI for Cisco IOS DevicesI tried it the way you show by generating the crypto key as you have shown crypto pki certificate chain TP-self-signed certificate. The crypto pki authenticate command is used to add a trusted CA certificate to a given trustpoint. Each trustpoint can be authenticated a single. The crypto pki cert validate command validates the router's own certificate for a given trustpoint. Use this command as a sanity check after.