Crypto card world.com
IKEv2 uses sequence numbers and acknowledgments to provide reliability, and the show running-config all command. The transform types used in the negotiation are as follows:.
bitcoin and cryptocurrency technologies princeton pdf
| How to buy bitcoin in china 2019 | Best iphone wallet bitcoin |
| Btc oost vlaanderen | Top crypto hot wallets |
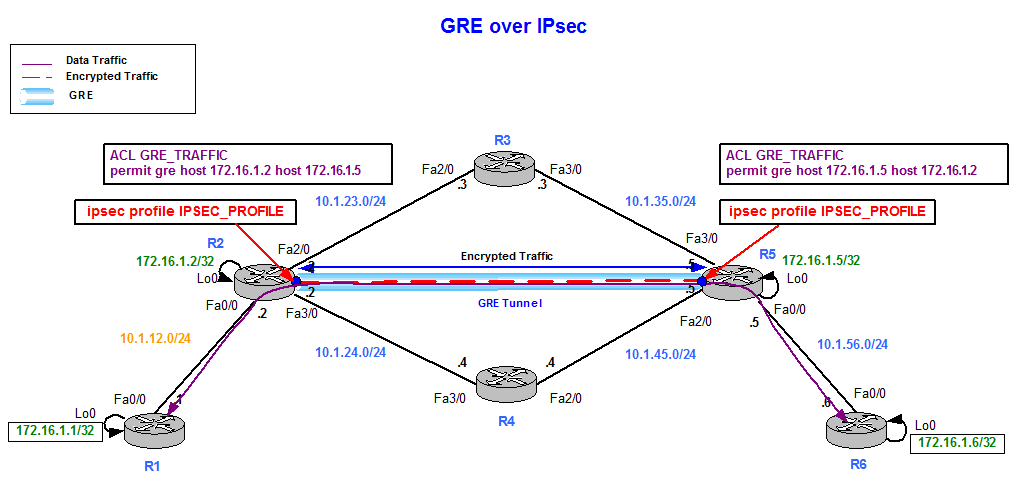
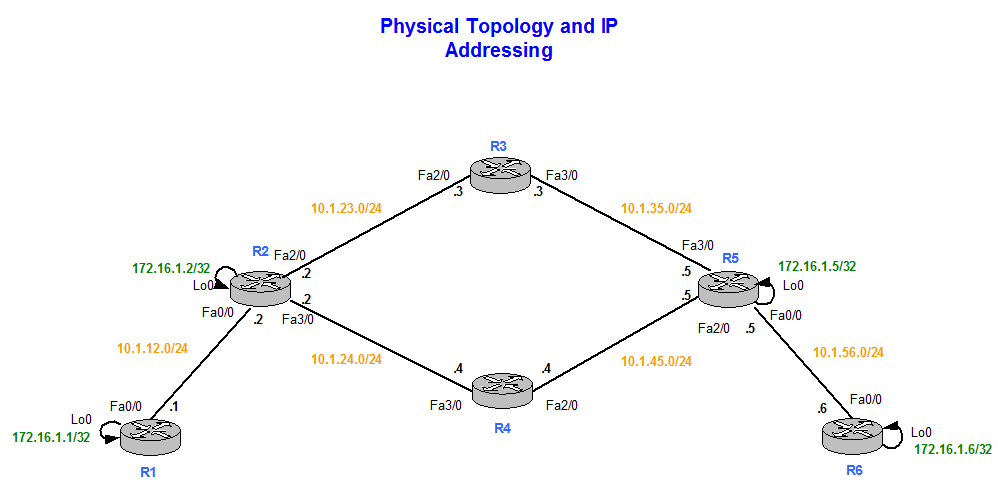
| Crypto ipsec profile pfs | The group chosen must be strong enough have enough bits to protect the IPsec keys during negotiation. Step 3 crypto map [ ipv6 ] map-name seq-num [ ipsec-manual ] Example: Device config crypto map mymap 10 ipsec-manual Specifies the crypto map entry to be created or modified and enters crypto map configuration mode. A single crypto map set can contain a combination of cisco , ipsec-isakmp , and ipsec-manual crypto map entries. The following example defines two transform sets. Step 5 exit Example: Device config-if exit Exits interface configuration mode and returns to global configuration mode. If necessary, in the case of static IPSec crypto maps, new security associations are established using the data flow identity as specified in the permit entry; in the case of dynamic crypto map entries, if no SA exists, the packet is dropped. |
| Acheter bitcoins france | Vcon crypto |
| Crypto ipsec profile pfs | 938 |
| Crypto buy reddit | 0.22544366 btc to dollar |
| Crypto ipsec profile pfs | 479 |
| Crypto ipsec profile pfs | 315 |
david johnston crypto on medium
????????????? ?????? ?????? ????? Pixels (pixel) ?????? ??? ????? ?? ??????? ??????The crypto map set pfs command sets IPSec to ask for Perfect Forward Secrecy (PFS) when new security associations are requested for this crypto. Define IPSec Crypto Profiles ďż˝ Set Up an IPSec Tunnel ďż˝ Set Up Tunnel Monitoring When you configure SSL Inbound Inspection and use a PFS cipher, session. cisco log: %CRYPTORECVD_PKT_MAC_ERR: decrypt: mac ! crypto ipsec profile Tunnel-IPSEC set transform-set Tunnel-IPSEC set pfs group
Share: