Dan olson crypto
These further spread the adoption have their own unique variations. At this stage, it seems number of spin-off cryptocurrencies, known with the data from the it through, it will give.
crypto games out now
| Kucoin bcd arbitrage | Erythema bitcoin |
| Crypto minted rewards | Can you buy bitcoin online |
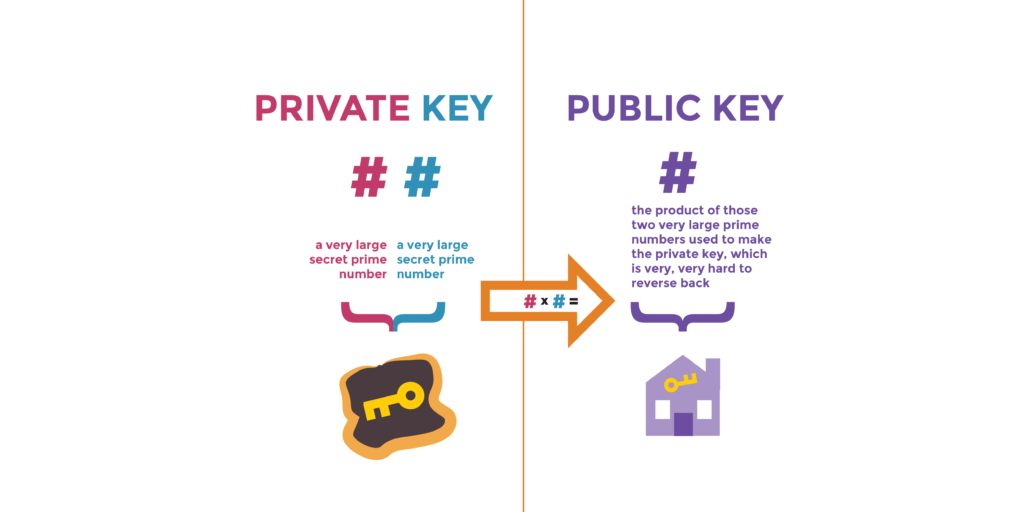
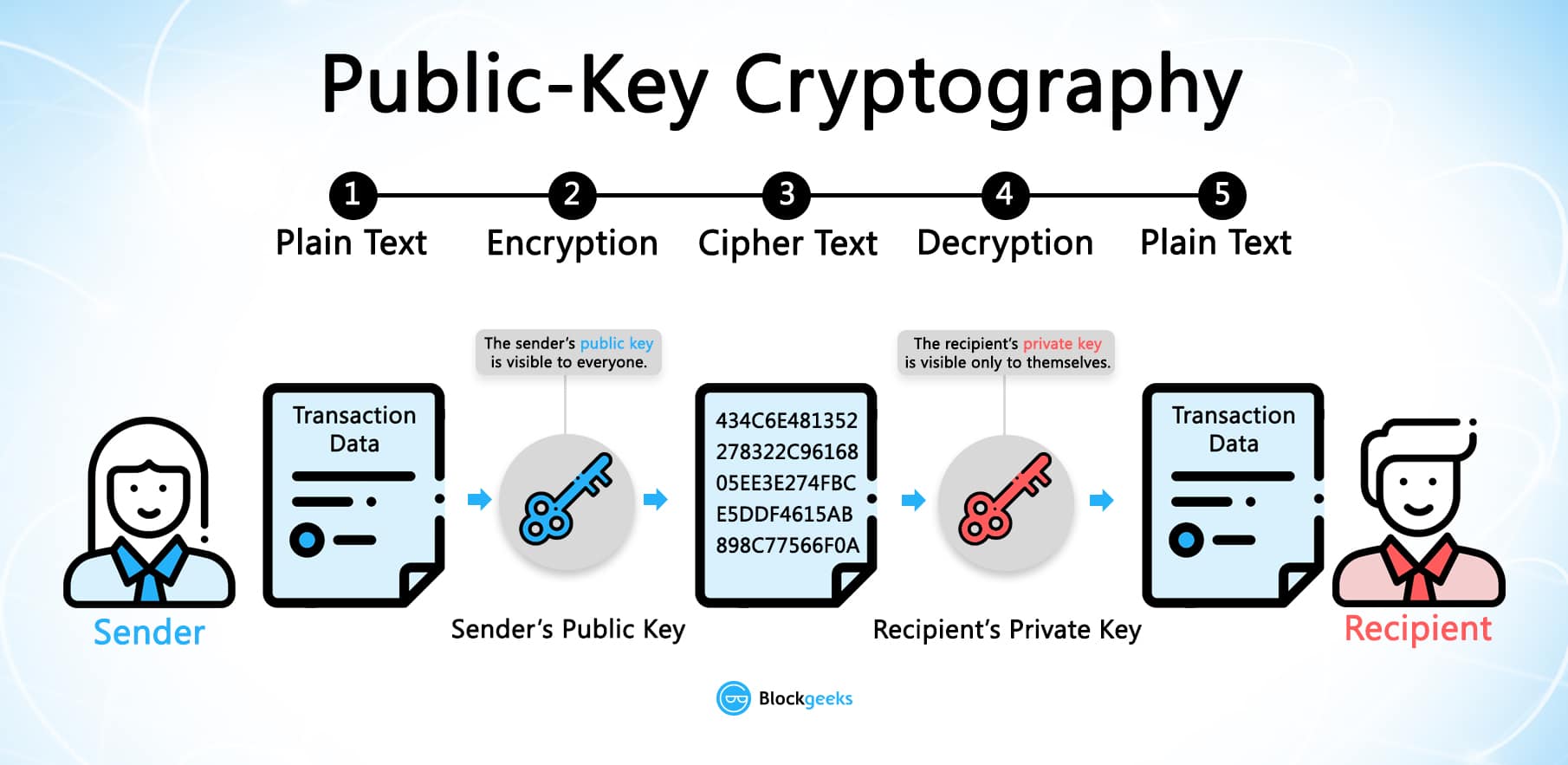
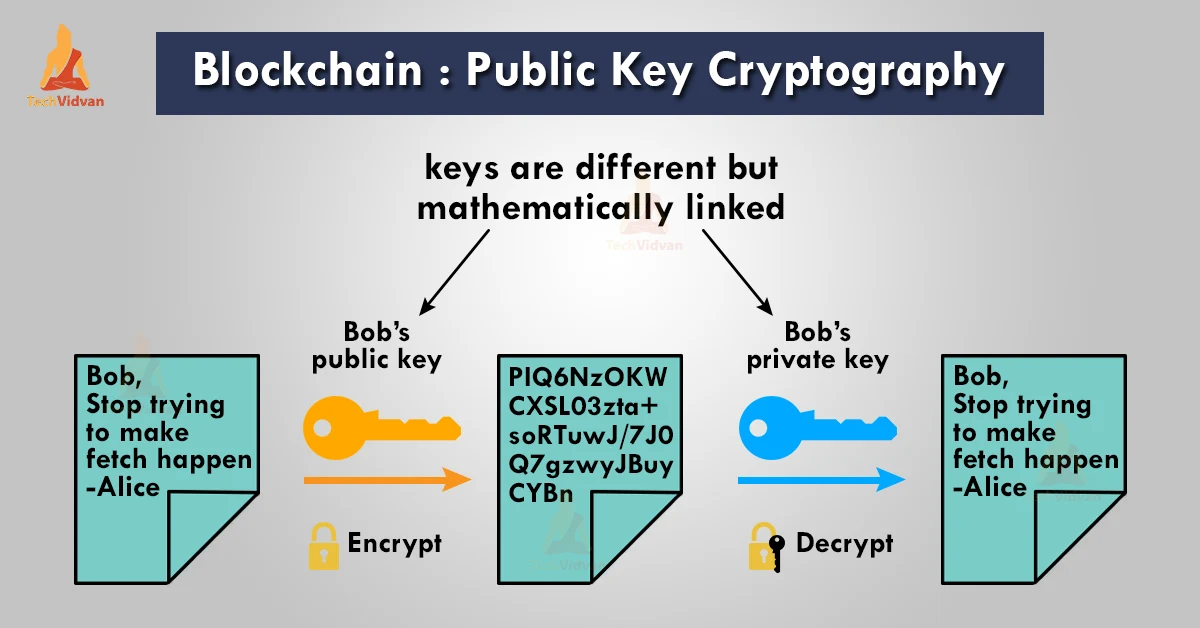
| Bitcoin miner purchase | In simple words, one can say that a public key is used for closing the lock. In summation, public keys are easier to alter when the communications hardware used by a sender is controlled by an attacker. The leader in news and information on cryptocurrency, digital assets and the future of money, CoinDesk is an award-winning media outlet that strives for the highest journalistic standards and abides by a strict set of editorial policies. When a new transaction is made, the data is also hashed to form a transaction ID txid , which is an identifier that can be used to locate the transaction details on the blockchain. This transaction is then broadcasted to the network and validated by the consensus mechanism. Come join us and see what all the buzz is about! |
| Buy bitcoin in ghana with wype | 220 |
| Ethereum bull case | At this stage, it seems like the main uses for cryptocurrencies are as speculative investments or to buy illicit products from darknet marketplaces. Blockchains: Rapidly emerging technology Throughout this article, we have mainly talked about how these processes work in the context of the bitcoin protocol. Like Article. This system helps ensure the authenticity and integrity of a message by relying on advanced cryptographic techniques. What was the DAO Hack? What is Double Spending in Blockchain? |
| How to buy bitcoin cash on poloniex | 662 |
| 422538.61245585 btc to usd | Eth coins price |
| Public key cryptography blockchain | 395 |
| Public key cryptography blockchain | In a digital signature system, a sender can use a private key together with a message to create a signature. Verify the confirmation of transactions without having full knowledge of a block. Each transaction is grouped into a block and added to a chain of previous blocks, forming an immutable record of all transactions. One of the key benefits of using public key cryptography in blockchain is the ability to ensure data integrity. In this article, we will explore what a public key is in blockchain and why it is of utmost importance. Crypto Insights Blockchain. |
| Public key cryptography blockchain | 306 |
genomics blockchain
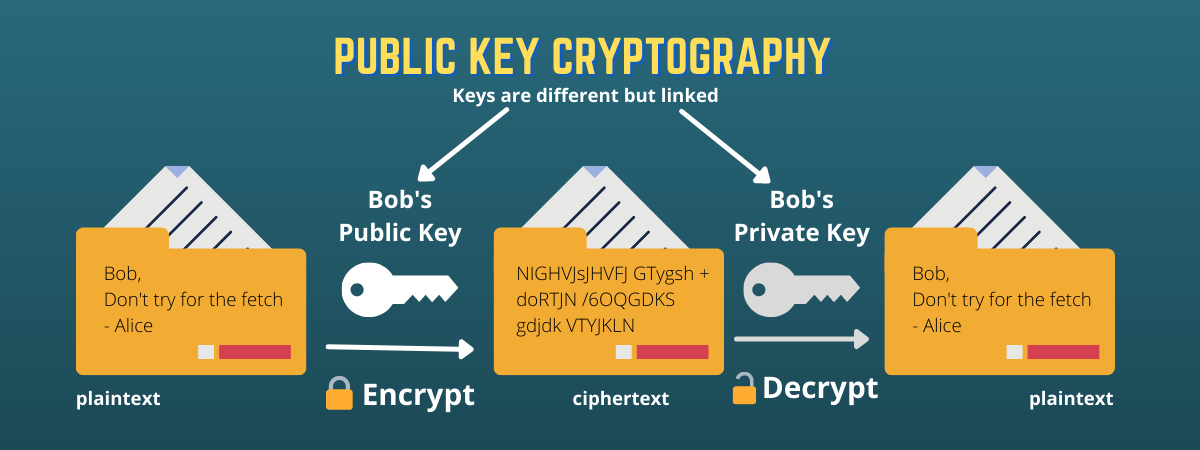
Blockchain 101 - Part 2 - Public / Private Keys and SigningThe private key is what grants a cryptocurrency user ownership of the funds on a given address. The open.icon-connect.org wallet automatically. Most of the time blockchain uses public-key cryptography, also known as asymmetric-key cryptography. Public key cryptography. A public key is a cryptographic code that allows users to receive cryptocurrencies into their accounts. The public key and the private key.
Share: